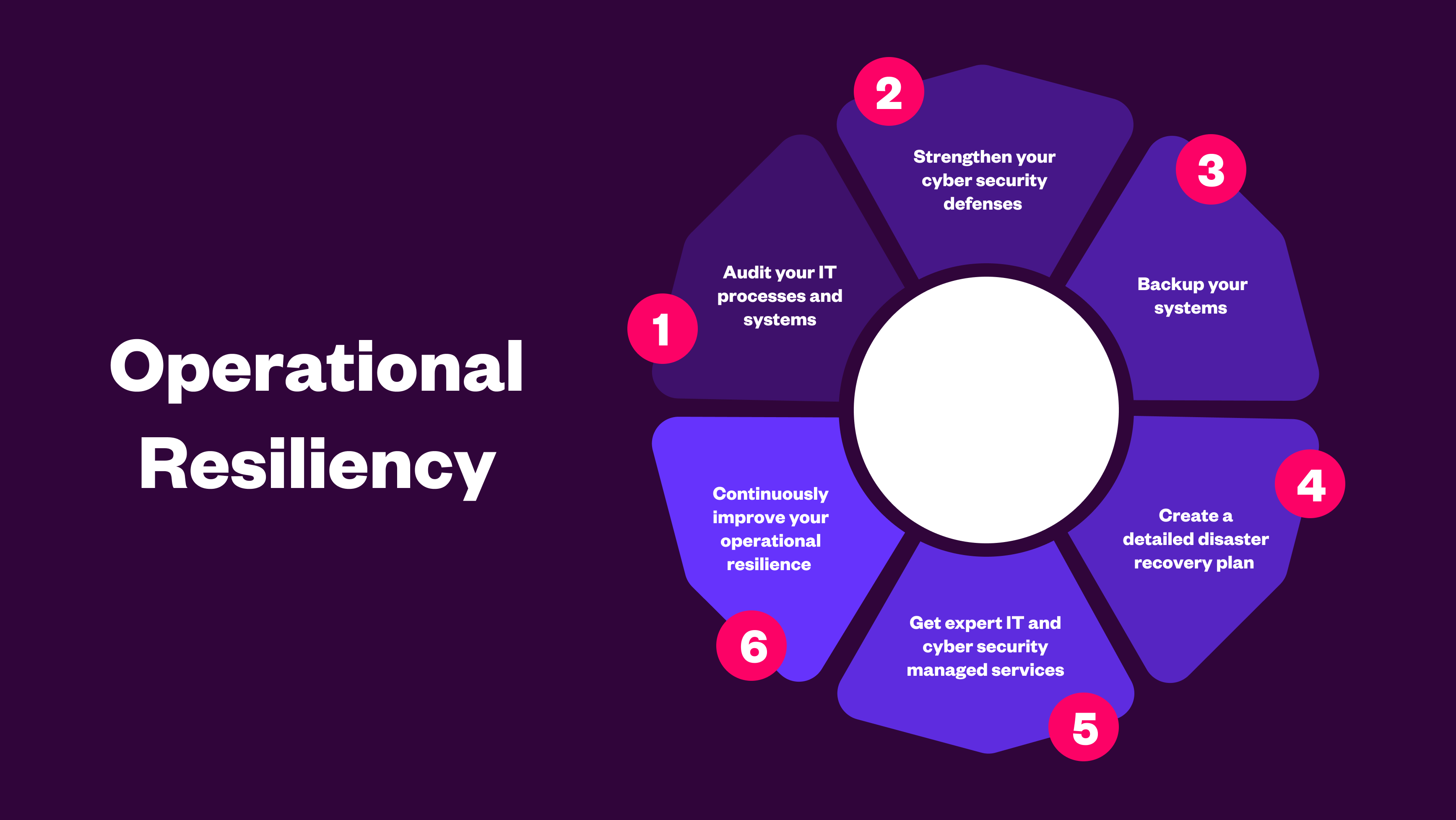
What Is Operational Resilience?
Learn how to build operational resilience against cyber threats, outages, and disruption, with best practices aligned to FCA, PRA, and DORA.
Secure data optimisation & proactive backup
Proactive Licensing, Compliance & Asset Management
Agile, Modular, & Secure Cyber Security & Managed Siem
Manage & Transform Multi-Cloud, Hybrid & On-Premise
-1.png?width=1920&height=1080&name=Photo%20graphic%20%20(1)-1.png)
Cyber threats and outages don’t discriminate, and IBM Power workloads are no exception. These mission-critical systems often run the applications that keep organizations moving, yet resilience strategies for IBM Power are frequently overlooked.
On November 12th, Jack Wilkins, Lead Engineering Consultant at Celerity, joined by Andrew Laidlaw from IBM, shared their insights on protecting these vital workloads.
During the session, attendees explored:
The evolving threat landscape for IBM Power systems
The true cost of data breaches
Why recovery of business-critical workloads is essential
What happens when recovery fails
The webinar also showcased Copy Assure, Celerity’s service designed to deliver validated, secure recovery for IBM Power environments, helping organisations ensure their systems are protected and recoverable.
Watch the webinar replay below to gain practical guidance and expert strategies for safeguarding your IBM Power workloads.
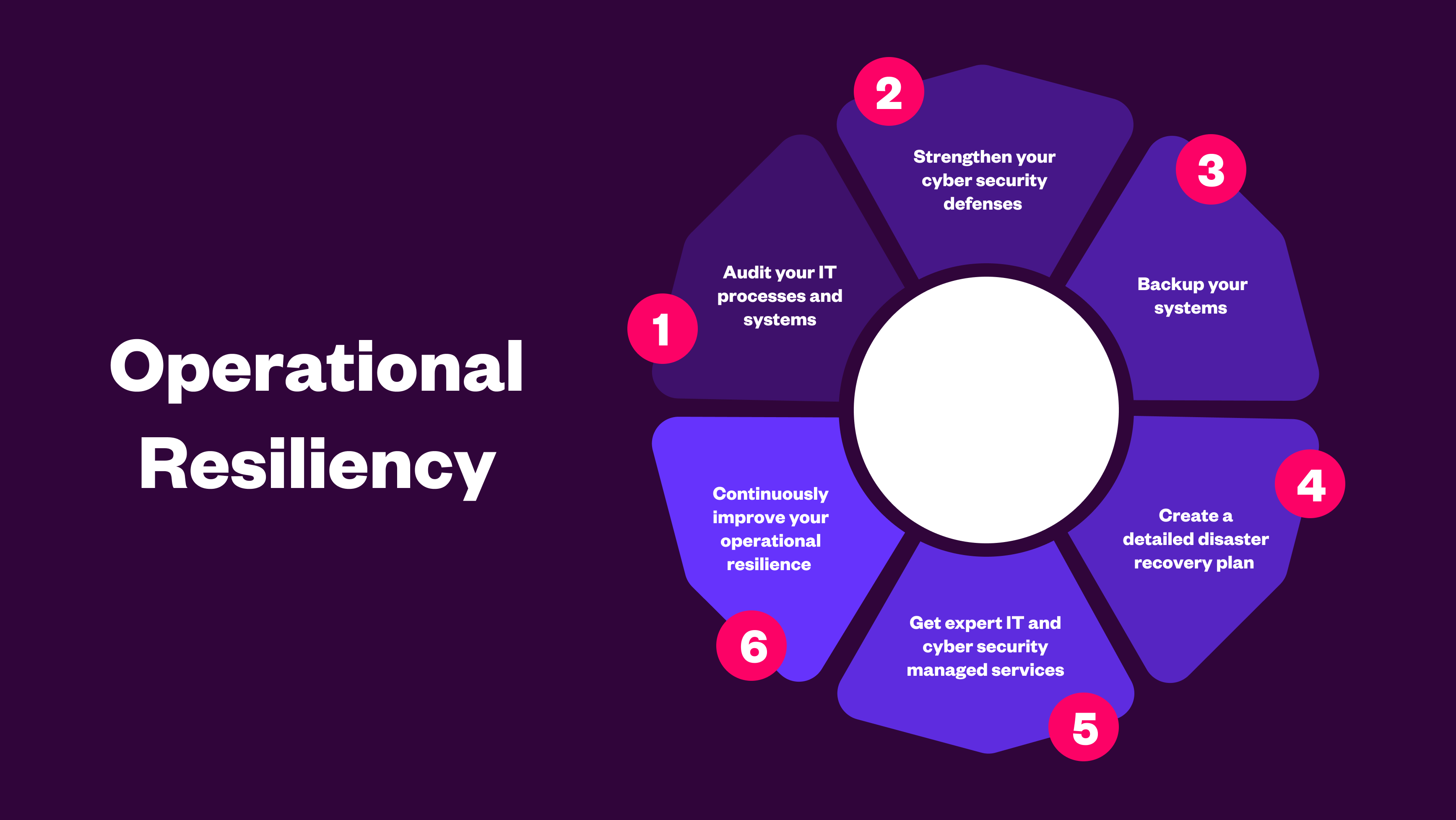
Learn how to build operational resilience against cyber threats, outages, and disruption, with best practices aligned to FCA, PRA, and DORA.
.png)
Vibe coding leads to reliance on familiar patterns, quick fixes, and unchecked dependencies. Learn how these hidden risks expose organisations to cybe...
.png)
AI in cyber security is critical to ensure you stay vigilant against evolving cyber threats, enhance team productivity, and maintain a robust security...
