Blog
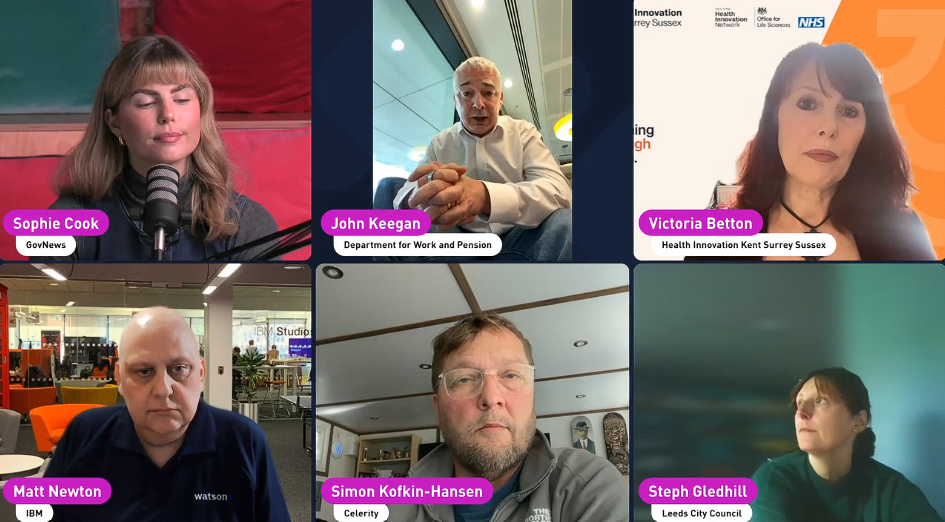
Here's What Public Sector Leaders Are Actually Doing to Scale AI
Software
Hannah Boswell
28 May 2026
Secure data optimisation & proactive backup
Proactive Licensing, Compliance & Asset Management
Agile, Modular, & Secure Cyber Security & Managed Siem
Manage & Transform Multi-Cloud, Hybrid & On-Premise
.png?width=1920&height=1080&name=blog%20images%20(8).png)
Ask most IT leaders whether their organisation has invested in cyber security and the answer is yes. Detection tools, backup solutions, incident response retainers, employee awareness training. The budgets are real and the intent is genuine.
But there is a question that rarely gets asked in the same conversation: is the infrastructure underneath all of that investment capable of performing when it is actually needed?
For many organisations, the answer is less clear than they would like.
Cyber security investment and cyber resilience are not the same thing. One is about preventing incidents. The other is about surviving them. And the difference often comes down to infrastructure.
There is an implicit assumption in most cyber resilience frameworks: that the infrastructure is adequate. The focus goes on the processes, the tooling, the people. Infrastructure is treated as a given.
This assumption is reasonable if your estate is current. It becomes a problem when key components are ageing, unsupported, or were simply never designed for the conditions a modern cyber incident creates.
And because infrastructure gaps don't generate alerts, they stay invisible. Your monitoring tools won't flag a server that's approaching end of support. Your backup software won't warn you that your storage array's restore throughput is insufficient for a full recovery under incident conditions. The gap only becomes visible when you need to rely on it.
A 50% increase in highly significant cyber incidents was reported by the NCSC in August 2025. Many involved organisations that had invested in security tools but hadn't stress-tested the infrastructure underneath them.
In 2025, a number of high-profile UK organisations suffered cyber incidents that tested their infrastructure far beyond normal operating conditions. Some faced weeks of disruption. Others saw factory shutdowns and significant revenue impact. In most cases, these weren't organisations that lacked security investment. They're examples of what happens when an incident is severe enough to test everything, including the infrastructure layer.
According to PwC, only 2 percent of companies surveyed had implemented firm-wide cyber resilience. The gap between security investment and actual resilience is significant, and it is showing up in incident outcomes.
The organisations that recovered fastest weren't simply those with the best detection tools. They were the ones whose infrastructure held up under pressure.
Is any of your infrastructure past end of support?
Hardware past its support window stops receiving firmware security updates. If your servers or storage arrays are running end-of-support firmware, known vulnerabilities are accumulating with no route to resolution. This applies to your recovery environment as much as your production environment.
Does your DR test reflect real incident conditions?
Most DR tests are conducted under controlled conditions that don't replicate a real incident. If your recovery test involves restoring a small number of systems in a low-pressure environment, you may not have tested how your storage infrastructure performs when it is restoring at scale under time pressure. The RTO in your plan and the RTO your hardware can deliver may not be the same number.
When did your infrastructure team last review the estate through a resilience lens?
Infrastructure reviews typically focus on capacity and performance. A resilience-focused review asks different questions: what fails under sustained load, what is running without firmware support, what would constrain a recovery. If that review hasn't happened recently, it is worth scheduling.
None of this is a suggestion that detection tools, backup software, or incident response planning aren't valuable. They are essential. The point is that they depend on an infrastructure layer that is capable of performing when called on.
Cyber security and infrastructure modernisation have traditionally been separate conversations with separate budgets. Increasingly, that separation is a liability. The organisations building genuine resilience are the ones treating infrastructure readiness as part of the cyber resilience picture, not a different conversation entirely.
You don't need a full infrastructure refresh project to start closing this gap. You need a clear picture of where your estate stands: lifecycle status, support windows, performance benchmarks, and what the gaps mean for your recovery capability.
That data is the foundation of an honest conversation about resilience. And it's the starting point for making infrastructure decisions that support your security investment, rather than quietly undermining it.
Celerity helps UK organisations understand where their infrastructure stands and what it means for their cyber resilience posture. Talk to an expert today.
Talk to an expert
Blog

28 May 2026

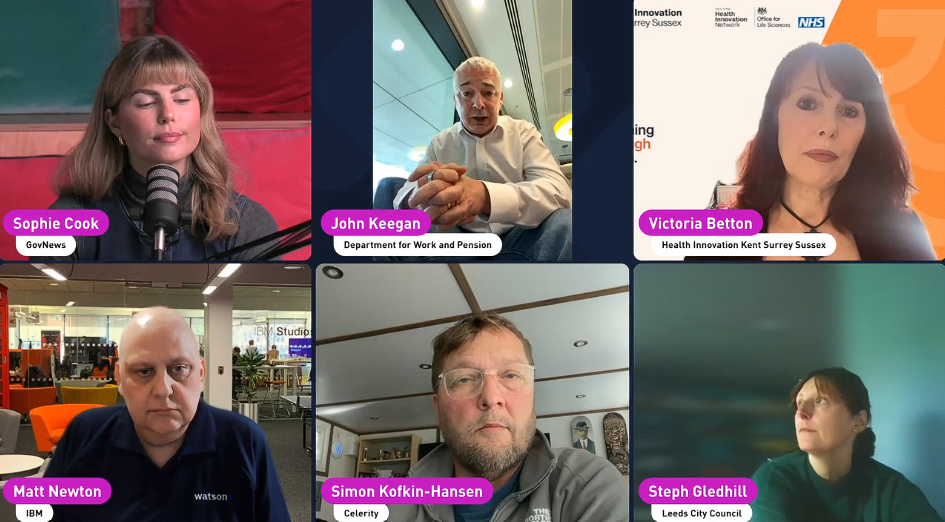
Video

19 May 2026
.png)
Blog
28 April 2026