Last week, yet another MOVEit breach victim was confirmed, an electronics household name suffered a significant cyber attack, and the hackers became the hacked! To learn more about each story, click the headings.
Flagstar Bank suffers a MOVEit data breach impacting over 800,000 customers
18/10
The US based Flagstar Bank has become yet another victim of the infamous MOVEit breaches, after confirming that Clop were the threat actors behind a May cyber attack. With the breach occurring between the 27th and and 31st of May, the criminals had managed to copy and transfer files from the compromised system before the incident was detected on the 3rd of June. In their filing with the Maine Attorney General, Flagstar Bank disclosed that 837,390 individuals were impacted - however, the bank's internal IT systems or core operations were never compromised or disrupted, and there is no evidence as of yet that the threat actors have misused the stolen information. According to New Zealand-based threat intelligence firm Emsisoft, the MOVEit breaches have now impacted over 2500 organisations around the world. (CPO Magazine)
Casio discloses data breach impacting customers in 149 countries
19/10
On the 11th October Japanese electronics giant Casio detected a data breach, disclosed last week, after hackers gained access to the servers of its ClassPad education platform and accessed customers' personal information. Fortunately, credit card information was not stored in the compromised database and the ClassPad.net app remains operational - threat actors failed to infiltrate Casio's systems beyond the compromised database within the development environment. In total, the criminals managed to access 91,921 Japanese records, and 35,049 records belonging to users from 148 different countries outside of Japan.
Casio have stated that ""At this time, it has been confirmed that some of the network security settings in the development environment were disabled due to an operational error of the system by the department in charge and insufficient operational management", adding ""Casio believes these were the causes of the situation that allowed an external party to gain unauthorised access."
Japan's Personal Information Protection Commission has been notified, and Casio is assisting authorities with their breach investigation. (Bleeping Computer)
Feel-good story of the week: Two ransomware gangs meet their demise
21/10
In a turn of events, last week the hackers became the victims with two ransomware operations taken offline.
The first group, Russia-based Trigona, surfaced in 2022 with close ties to BlackCat and CryLock. Trigona primarily targeted organisations in the US and India, typically compromising MYSQL servers with brute-force password attacks and a technical sophistication that was considered "mixed". Last week, the content on Trigona's dark web site was taken down and wiped by a group named the Ukrainian Cyber Alliance, with the content replaced by a banner reading “Trigona is gone! The servers of Trigona ransomware gang has been infiltrated and wiped out". A social media post from the Ukrainian Cyber Alliance added that the group had wiped out Trigona’s “landing, blog, leaks site, internal server (rocketchat, atlassian), wallets and dev servers.”.
Ragnar Locker was the second ransomware group taken down last week, a Ransomware-as-a-Service operation infamous for its success in hacking organisations within a variety of sectors including health care, government, technology, finance, education, and media. A statement from Europol on Friday said "In an action carried out between 16 and 20 October, searches were conducted in Czechia, Spain and Latvia. The “key target” of this malicious ransomware strain was arrested in Paris, France, on 16 October, and his home in Czechia was searched. Five suspects were interviewed in Spain and Latvia in the following days. At the end of the action week, the main perpetrator, suspected of being a developer of the Ragnar group, has been brought in front of the examining magistrates of the Paris Judicial Court.
The ransomware’s infrastructure was also seized in the Netherlands, Germany and Sweden and the associated data leak website on Tor was taken down in Sweden." (Ars Technica)
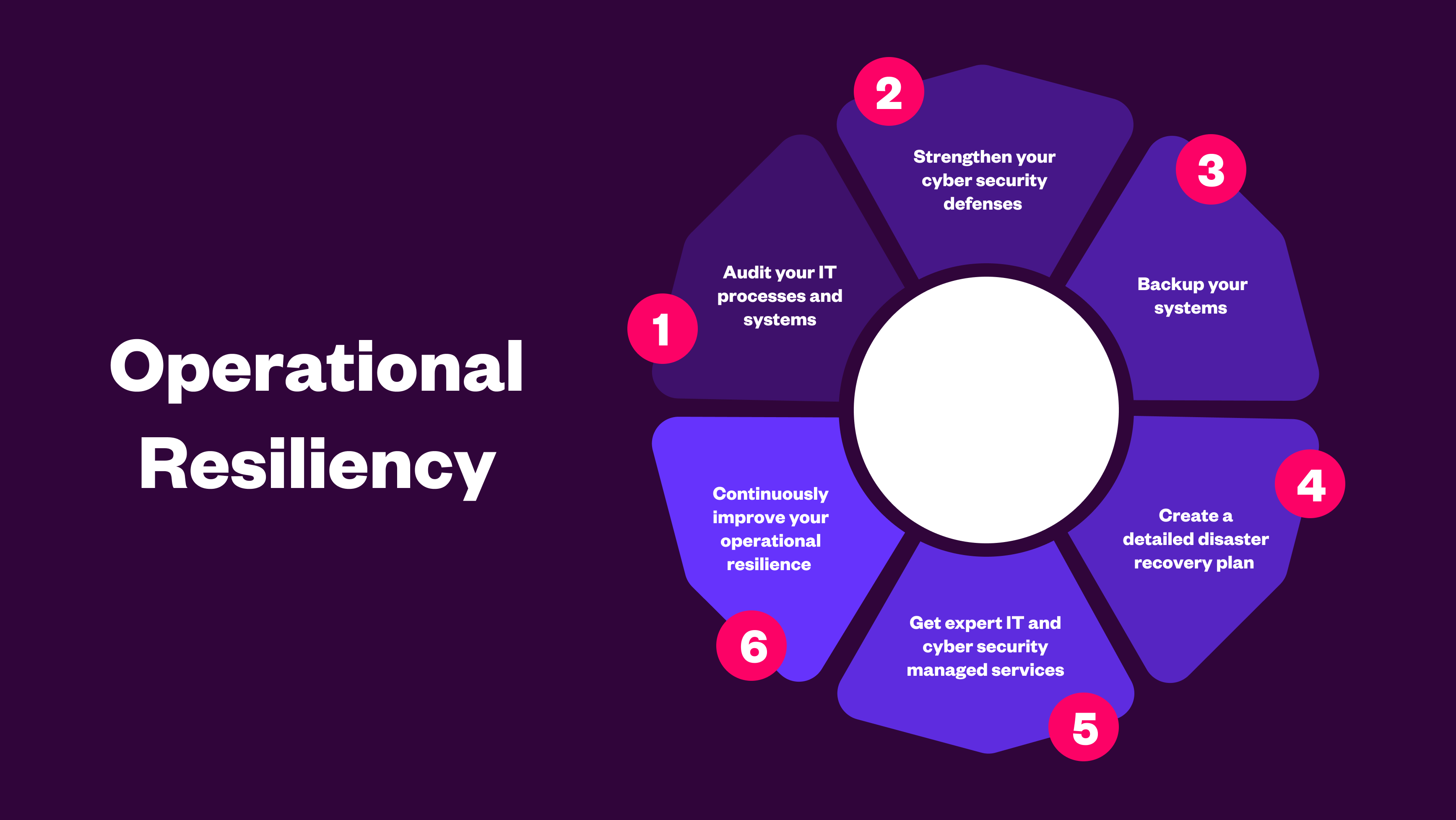
Attempted cyber attacks occur every second, and as we can see from the recent headlines, constantly change in nature. It's critical that your organisation is as protected as possible from all forms of cyber crime, so Contact Celerity to find out how our layered approach to cyber security could protect your business!


.png)
.png)