What Is Operational Resilience?
Learn how to build operational resilience against cyber threats, outages, and disruption, with best practices aligned to FCA, PRA, and DORA.
Secure data optimisation & proactive backup
Proactive Licensing, Compliance & Asset Management
Agile, Modular, & Secure Cyber Security & Managed Siem
Manage & Transform Multi-Cloud, Hybrid & On-Premise
A cyber security managed service provider delivers continuous, expert-led protection
Core services include SIEM, MDR, exposure management, consultancy, and SOC access
Unified security operations improve resilience and reduce risk
Proactive strategies help prevent threats before they impact the business
Celerity provides a full-service, future-ready cyber security solution
This article breaks down each core component, explains how they work together, and highlights what to look for in a future-proof managed cyber security service.
Managed cyber security solutions are designed to provide continuous, expert-led protection against cyber threats. A cyber security managed service provider combines advanced technology, skilled professionals, and proven processes to detect threats early, respond quickly, and continuously strengthen your organisation’s security posture.
Rather than relying on one-off tools or reactive controls, this approach ensures long-term resilience and operational efficiency.
At their core, complete managed cyber security solutions typically include:
24/7 threat monitoring via managed SIEM
Rapid incident response with managed detection and response services
Proactive exposure management
Cyber security consultancy and compliance
Access to skilled security professionals through a Security Operations Centre (SOC).
When all these components are executed together in a unified way, they help organisations reduce risk, improve resilience, and meet regulatory expectations.
Continuous threat monitoring is the foundation of any service offered by a cyber security managed service provider.
A managed Security Information and Event Management (SIEM) platform collects and correlates data from sources such as endpoints, networks, and cloud infrastructure.
This ensures that:
Genuine threats are identified quickly
Alert fatigue is reduced
Critical alerts are prioritised and addressed
With round-the-clock monitoring, organisations benefit from immediate detection and response to emerging threats. Celerity enhances this process with intelligent automation and expert oversight.
Detection alone is not enough. You have to be able to act rapidly.
Managed detection and response services mean that alerts are swiftly investigated, validated, and acted on quickly to contain threats.
A robust MDR capability includes:
Clear Response Frameworks: Defined escalation paths and decision-making authority
Full Incident Lifecycle Management: From detection to remediation and post-incident review
Reduced Business Impact: Faster containment limits damage and downtime
Celerity ensure that every stage of the response process is handled efficiently and effectively.
A modern cyber security managed service provider goes beyond traditional endpoint protection by delivering proactive exposure management goes well beyond traditional endpoint controls to provide unified visibility and real-time risk insight.
Rather than reacting to individual alerts or isolated vulnerabilities, exposure management continuously identifies, assesses, and prioritises exposures so you can reduce risk before it can be exploited.
A sophisticated strategy combines multiple advanced capabilities to strengthen your security posture against both internal and external threats.
Ongoing monitoring and live data analysis provide immediate visibility into emerging risks across your environment.
Intelligent analytics help prioritise vulnerabilities based on real-world risk, allowing faster and more effective decision-making.
This includes understanding how attackers may view your digital footprint, as well as uncovering hidden risks within systems, networks, and infrastructure.
Exposure management also addresses vulnerabilities caused by human behaviour, including phishing and social engineering threats.
Proactive exposure management enables your security team to focus on the areas that matter most.
It reduces exploitable risk and supports faster, more informed responses to evolving threats, forming a critical part of a comprehensive service delivered by Celerity.
Technology alone is not enough. Strategic guidance ensures that security aligns with business goals.
Cyber security consultancy ensures that your cyber security strategy aligns with organisational risk, regulatory obligations, and business priorities for maximum commercial impact. This is where executive and technical priorities begin to overlap.
Cyber security consultancy provided by a cyber security managed service provider supports:
Regulatory compliance including Cyber Essentials, ISO 27001, and NCSC guidance
Alignment between technical controls and business priorities
Audit readiness through continuous evidence generation
Celerity helps organisations turn compliance into a by-product of effective security operations rather than a reactive exercise.
At the centre of a full-service managed cyber security solution is access to experienced security professionals.
A Security Operations Centre (SOC) provides Human-led analysis
Decision-making
Expert oversight, powered by AI for optimal efficiency, across monitoring, response and continuous improvement.
Skilled analysts apply judgement, context, and experience to interpret alerts accurately and respond effectively to real-world threats. Celerity combines human expertise with AI-driven efficiency to deliver superior outcomes.
A full-service solution operates as a continuous cycle:
SIEM monitoring detects threats
MDR services respond rapidly
Exposure management reduces risk proactively
SOC analysts provide expert oversight
Consultancy ensures alignment with business and regulatory needs
This integrated approach strengthens resilience and ensures consistent improvement across all security functions.
For executives and senior stakeholders, the value of a working with a cyber security managed service provider is measured through outcomes.
A full-service managed cyber security solution delivers:
Reduced Cyber Risk: Continuous monitoring and proactive strategies minimise the likelihood and impact of cyber threats.
Faster Incident Containment: Rapid detection and response capabilities significantly reduce dwell time and limit disruption.
Reputational Protection: Strong security practices help safeguard brand trust and customer confidence.
Confidence in Compliance: Ongoing alignment with regulatory requirements ensures compliance is handled effectively, reducing the risk of unexpected penalties.
A leading cyber security managed service provider provides transparency, accountability, and continuous improvement.
This gives executives the clarity needed to make informed decisions around risk management, investment, and long-term business resilience, with Celerity supporting every stage of that journey.
From a technical standpoint, cyber resilience is demonstrated through high-quality detection logic, clearly defined response authority, and meaningful KPIs such as time-to-detect and time-to-contain.
Full-service cyber security providers embed learning loops that ensure continuous improvement of your cyber security posture.
Not all providers are equal.
A mature cyber security managed service provider demonstrates:
Measurable performance improvements
Reduction in repeat incidents
Continuous optimisation through feedback loops
Clear ownership of decision-making
Celerity stands out by delivering a holistic, enterprise-grade solution that evolves alongside your organisation.
Choosing the right partner is critical. Celerity offers:
End-to-end managed cyber security services
Expert-led SOC operations
Proactive, intelligence-driven security strategies
Scalable solutions tailored to your business
If you are looking for a reliable cyber security managed service provider, Celerity offers the expertise, technology, and strategic insight needed to protect your organisation and support long-term growth.
Talk to our cyber security experts today to discover how Celerity can transform your cyber security strategy.
Further reading: Check out our managed cyber security case study with Royal Papworth Hospital.
A cyber security managed service provider delivers continuous monitoring, threat detection, incident response, and strategic guidance to protect organisations from cyber threats.
They provide expert support, reduce internal workload, improve threat response times, and enhance overall security posture.
Celerity aligns your security strategy with frameworks such as ISO 27001 and Cyber Essentials, ensuring continuous compliance and audit readiness.
MDR includes threat detection, investigation, containment, remediation, and post-incident analysis.
Look for proven expertise, transparent reporting, proactive capabilities, and a provider like Celerity that offers a full-service, integrated approach.
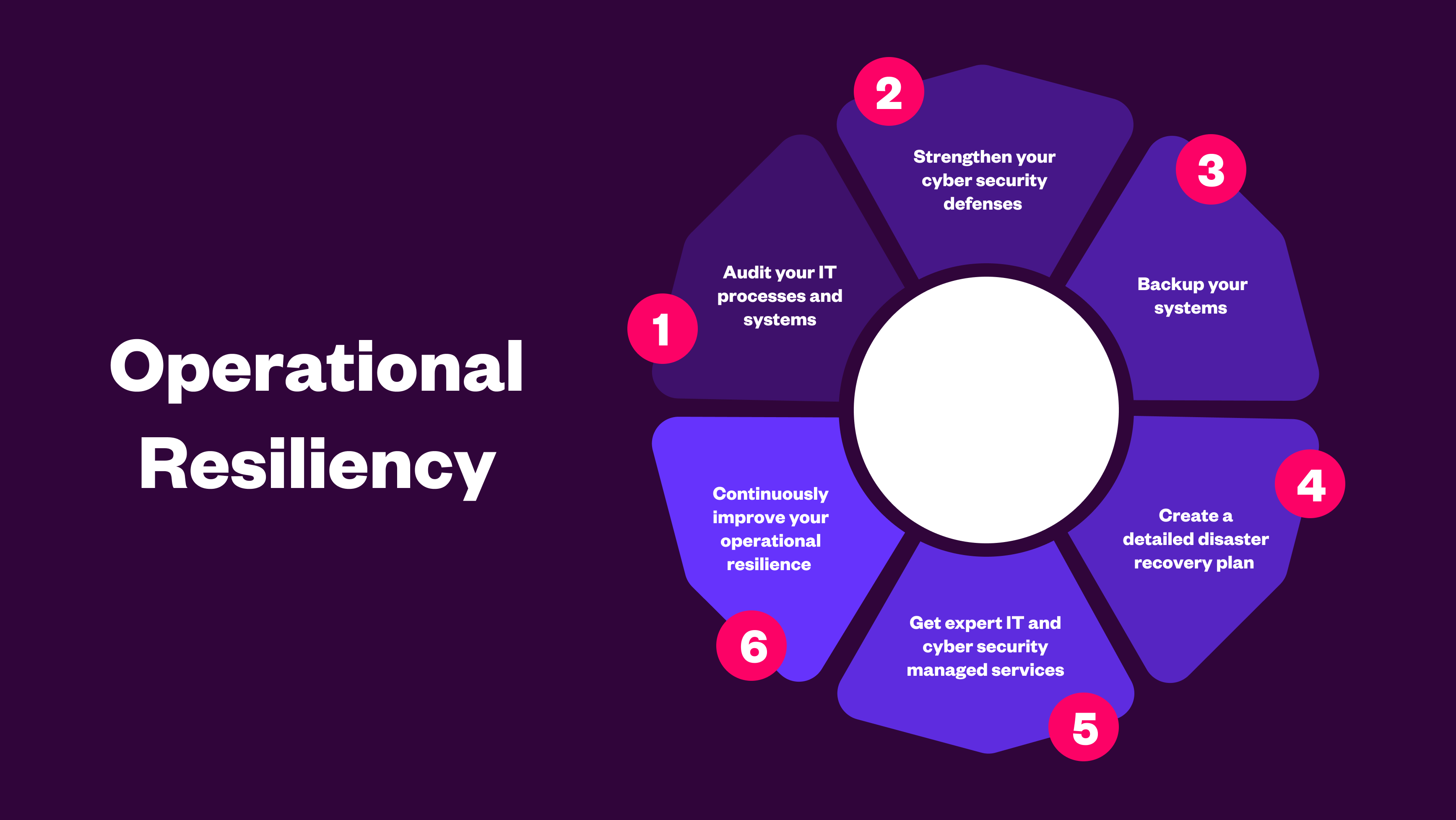
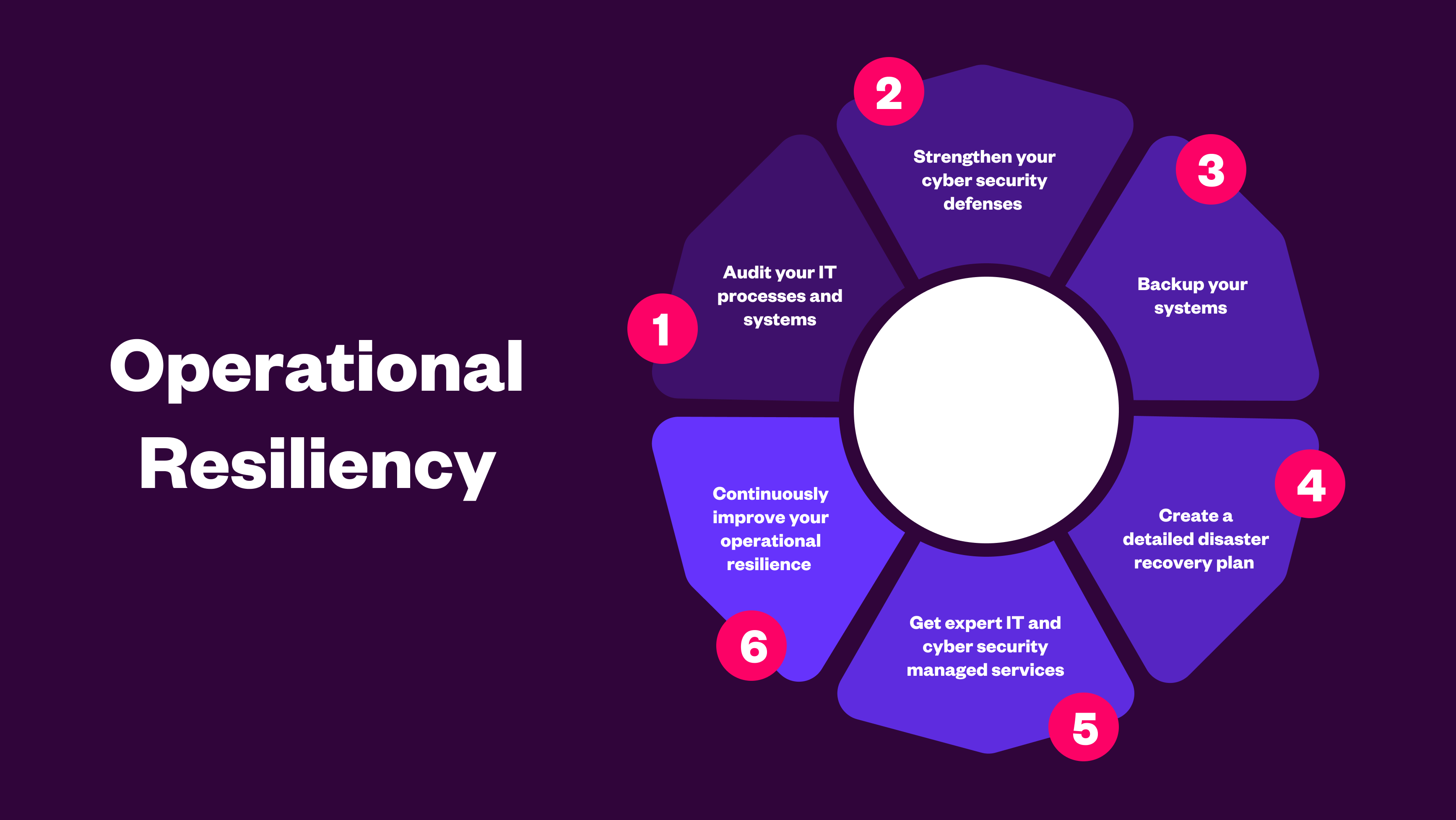
Learn how to build operational resilience against cyber threats, outages, and disruption, with best practices aligned to FCA, PRA, and DORA.
.png)
Vibe coding leads to reliance on familiar patterns, quick fixes, and unchecked dependencies. Learn how these hidden risks expose organisations to cybe...
.png)
AI in cyber security is critical to ensure you stay vigilant against evolving cyber threats, enhance team productivity, and maintain a robust security...
