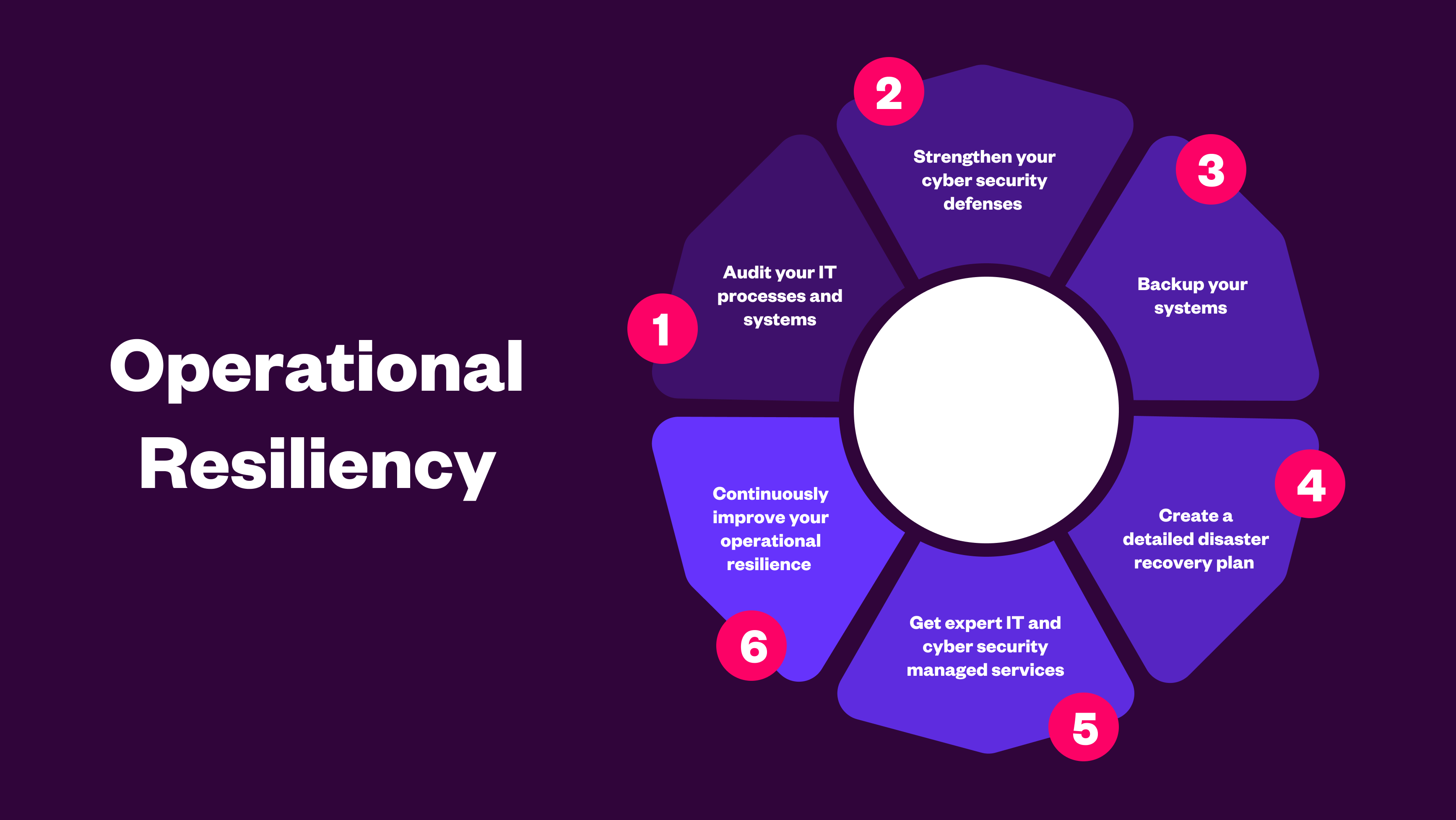
What Is Operational Resilience?
Learn how to build operational resilience against cyber threats, outages, and disruption, with best practices aligned to FCA, PRA, and DORA.
Secure data optimisation & proactive backup
Proactive Licensing, Compliance & Asset Management
Agile, Modular, & Secure Cyber Security & Managed Siem
Manage & Transform Multi-Cloud, Hybrid & On-Premise
There’s a cyber threat already active against public sector organisations that most security leaders haven’t fully accounted for yet. It doesn’t look like a breach. It won’t trigger your SIEM. And you won’t know it’s happened until it’s too late to do anything about it.
Bad actors are harvesting encrypted data right now, government records, citizen data, sensitive communications, clinical information, banking on the fact that quantum computers will be able to decrypt it within the next decade. By the time Q-Day arrives, the data is already gone. The window to protect it is now.
The assumption that quantum is a tomorrow concern is the most dangerous position a public sector organisation can take. The encryption protecting your data today was designed for a world where classical computers would take millions of years to break it. Quantum computers will do it in minutes.
The NCSC has been unambiguous: high-risk systems should migrate to post-quantum cryptography by 2030, with complete migration across all systems by 2035. That sounds like runway. It isn’t… not when you factor in the complexity of government and public sector infrastructure, the prevalence of legacy systems, and the time it takes to map cryptographic dependencies before you can even start migrating them.
The organisations that treat 2030 as their start date will miss it. The ones that start now have a realistic chance of hitting it.
This isn’t a theoretical attack vector. It’s already happening. State-sponsored actors and sophisticated criminal groups are systematically collecting encrypted data from high-value targets like government agencies, healthcare organisations, defence supply chains and research institutions with the explicit intention of decrypting it once quantum capability reaches the required threshold.
What makes public sector data particularly attractive is its longevity. A citizen’s record, a classified communication, genomic data, long-term research, this information retains its value for decades. The attacker doesn’t need to be able to read it today. They just need to have it.
By the time Q-Day arrives, any data that hasn’t been protected with quantum-safe encryption is already compromised in all but name.
In our experience working with public sector organisations on data security, the picture is consistent. Awareness of the quantum threat has increased significantly, particularly following the NCSC guidance and the UK government’s investment in quantum computing. But awareness hasn’t translated into readiness.
The three gaps that come up most often are:
Quantum readiness falls between IT security, infrastructure, and procurement — and ends up owned by none of them. Without a named individual responsible for driving the programme, and the seniority to get decisions made, it stalls.
Most organisations don’t have a clear map of where encryption is used across their systems, which algorithms are protecting which data, or which third-party tools and supply chain dependencies introduce cryptographic risk. You can’t migrate to quantum-safe encryption without this picture. Building it takes longer than organisations expect, particularly in complex or legacy-heavy environments.
The majority of public sector organisations rely heavily on third-party technology. If your suppliers haven’t started their quantum-safe roadmap, your migration timeline is constrained by theirs. Most organisations haven’t had this conversation yet.
1. Establish ownership. Identify a senior leader to champion quantum readiness and give them a small dedicated team. This is a strategic risk programme, not an IT ticket.
2. Map your cryptographic landscape. Understand where encryption is used, what algorithms are in play, and which systems handle your most sensitive and longest-lived data. This is your baseline.
3. Prioritise by risk and data longevity. Focus first on the systems where a future breach would have the greatest impact. Records that will remain sensitive for decades, systems handling citizen or patient data, and critical operational infrastructure.
4. Engage your technology suppliers. Ask them directly: what is your post-quantum cryptography roadmap, and what timeline are you working to? Their answer will shape yours.
5. Plan for crypto-agility. The post-quantum cryptography standards are still evolving. Build the flexibility to adapt your security posture as the landscape changes, rather than locking into a single approach.
Research from IBM suggests most organisations anticipate needing around 12 years to become fully quantum-safe. The NCSC’s 2035 deadline for complete migration reflects that reality. But the 2030 target for high-risk systems is only four years away and the planning, assessment and supplier engagement work needs to start well before the migration itself.
The good news is that starting now doesn’t require a massive upfront investment. It requires clarity on ownership, a realistic assessment of where you are, and a plan that builds momentum over time. The organisations that will struggle are the ones that keep treating it as a future problem.
We work with public sector organisations on the data security and resilience programmes that quantum readiness sits within, helping organisations understand their current exposure, map their cryptographic dependencies, and build a practical path to quantum-safe security.
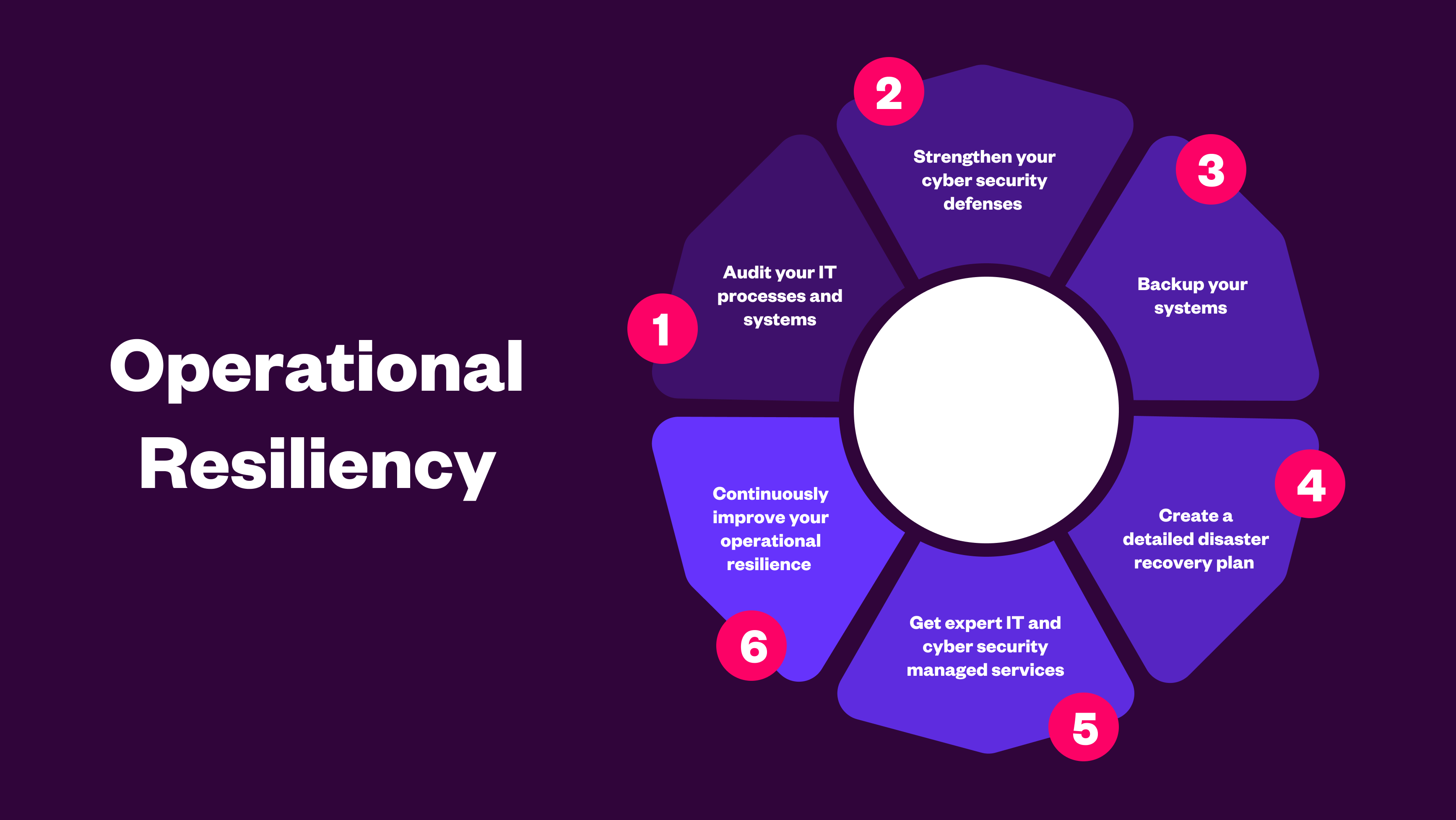
Learn how to build operational resilience against cyber threats, outages, and disruption, with best practices aligned to FCA, PRA, and DORA.
.png)
Vibe coding leads to reliance on familiar patterns, quick fixes, and unchecked dependencies. Learn how these hidden risks expose organisations to cybe...
.png)
AI in cyber security is critical to ensure you stay vigilant against evolving cyber threats, enhance team productivity, and maintain a robust security...
