What Is Operational Resilience?
Learn how to build operational resilience against cyber threats, outages, and disruption, with best practices aligned to FCA, PRA, and DORA.
Secure data optimisation & proactive backup
Proactive Licensing, Compliance & Asset Management
Agile, Modular, & Secure Cyber Security & Managed Siem
Manage & Transform Multi-Cloud, Hybrid & On-Premise
Immutability is not a replacement for operational resilience. Before relying on immutability, it is critical to understand what it protects and what gaps it leaves in your security posture.
Immutable backups are often presented as the ultimate defence against cyber threats and breaches. They are described as untouchable, unchangeable, and guaranteed to survive an attack. It’s no wonder then, that 94% of IT leaders rely on them to safeguard their data.
However, the term “immutable” can be generic and often misinterpreted. Different vendors mean different things by it, and the protection it provides depends heavily on how it is implemented, governed, and tested.
Many organisations believe they are protected from ransomware because they have been told their backups are immutable. Incident response experience often tells a different story.
Backups may technically be immutable, but still inaccessible, compromised through privileged access, being too slow to restore, or becoming unusable when the business needs them most.
This is where resilience can be challenged.
Several common misunderstandings are associated with immutable backups, including:
Immutability is treated as a guarantee
The word “immutable” is often interpreted as absolute. The assumption is that if backups are immutable, they cannot be affected by ransomware under any circumstances.
Immutability is conditional. It applies within defined systems, under specific configurations, and for a set of retention periods. It does not remove all attack paths.
Immutability is confused with resilience
There is a widespread belief that immutable backups automatically make an organisation ransomware resilient.
Resilience requires more than preserved data. It depends on access controls, isolation, recovery capability, testing, and the ability to restore critical services within acceptable timeframes. Immutability supports resilience, but it does not deliver it on its own.
Logical controls are assumed to be untouchable
If attackers gain privileged access, they may be able to alter retention policies, disable protections, or delete repositories before launching an attack.
Immutability is only as strong as the identity and access controls around it.
Immutable is assumed to mean clean
Another common assumption is that immutable backups are automatically safe to restore.
They are not. Backups can be immutable and still contain dormant malware, misconfigurations, or corrupt data. Immutability preserves the state of data at the time it was captured, including any problems already present.
Without verification and recovery testing, immutability can simply preserve a bad state very effectively.
Marketing language vs technical reality
In everyday language, “immutable” means something that cannot be changed - full stop. When that word is used, it creates an expectation of absolute protection. For non-specialists and senior decision-makers, the implication is often that ransomware simply cannot affect immutable backups.
However, this is not the case.
In technical terms, immutability is always scoped, conditional, and dependent on correct configuration and governance. Those caveats are rarely front and centre in marketing conversations.
As a result, organisations may:
Assume backups are safe without verifying recovery
Reduce focus on restore testing
Underestimate the impact of credential compromise
Treat immutability as a substitute for resilience planning
This leaves significant gaps in your security posture.
Immutable backups are backups that cannot be altered or deleted for a set period of time.
The intention is to protect against:
Ransomware encrypting backup data
Malicious deletion by attackers
Accidental deletion by administrators
What this does not automatically guarantee is that the backups are secure, isolated, malware-free, or recoverable within an acceptable timeframe.
Immutability protects stored data but is not responsible for the entire recovery outcome.
In real attacks, backups can fail because immutability was incomplete, not because they weren’t immutable in the first place.
Common failure points include:
Compromised backup administrator credentials
Retention settings altered before encryption
Backups preserved in an infected state
Recovery times exceeding business impact tolerances
Restore processes that have never been tested under pressure
In these cases, backups may technically be immutable but still fail to protect the business.
A more useful question than “Are our backups immutable?” is:
Can we restore our most critical services within an acceptable timeframe, even after a cyber-attack or breach?
This shifts the focus from a check-box exercise to outcomes, and from technology to business impact. It also aligns backup strategy with broader Operational Resilience expectations.
Immutable backups support Operational Resilience, but they do not define it.
True resilience also requires:
Clear identification of critical services
Agreed impact tolerances
Tested recovery processes
Strong governance and oversight
Continuous assurance that controls work in practice
Backups that cannot be changed but also cannot be restored still compromise resilience.
Immutable backups are not a guarantee. They are a design choice that only delivers value when supported by strong access controls, isolation, governance, and regular recovery testing.
If you’re taking your immutable backups at face value, then it’s essential to scrutinise them further to ensure your organisation stays operationally resilient. Find out more about our managed backup service here.
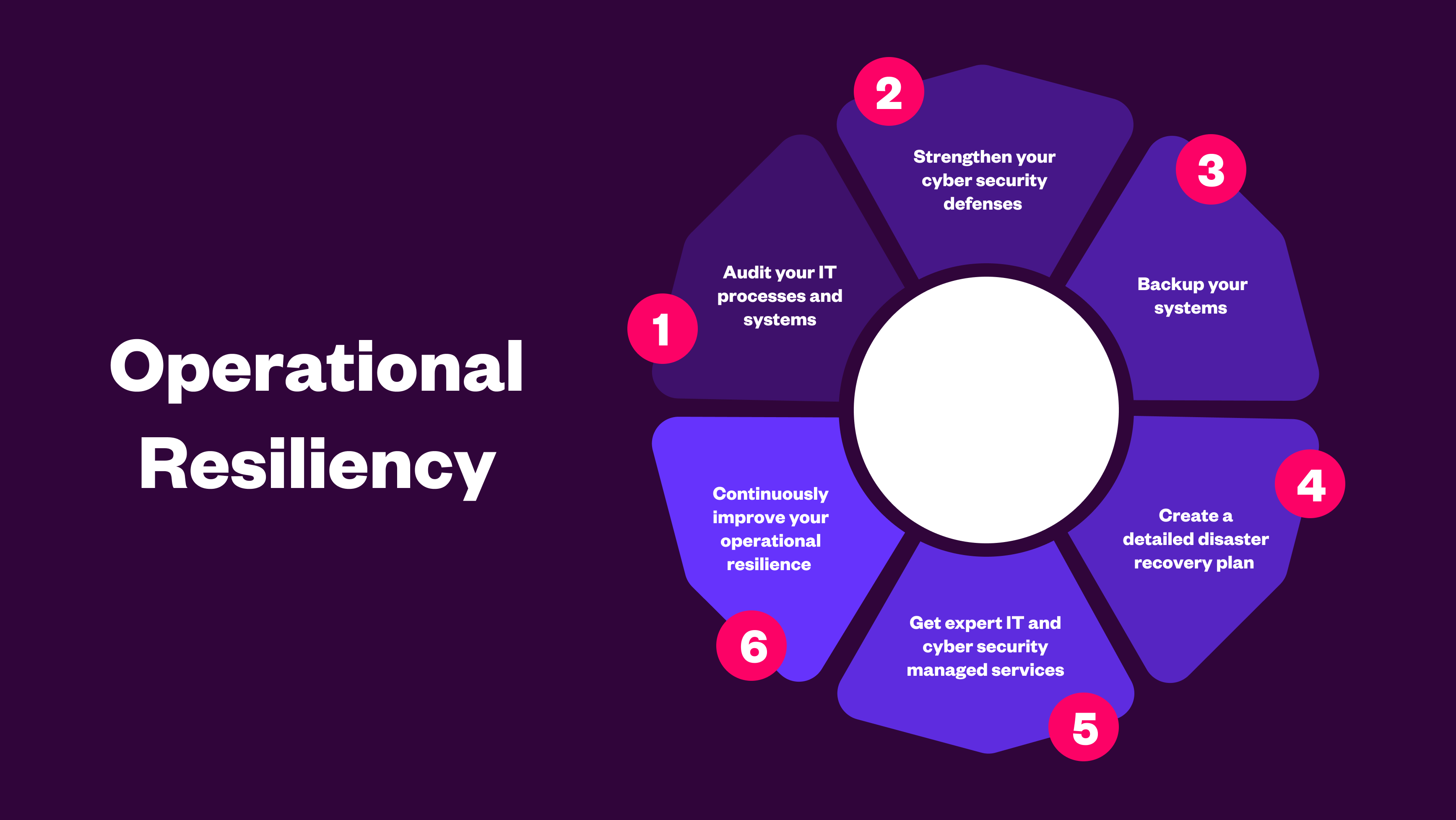
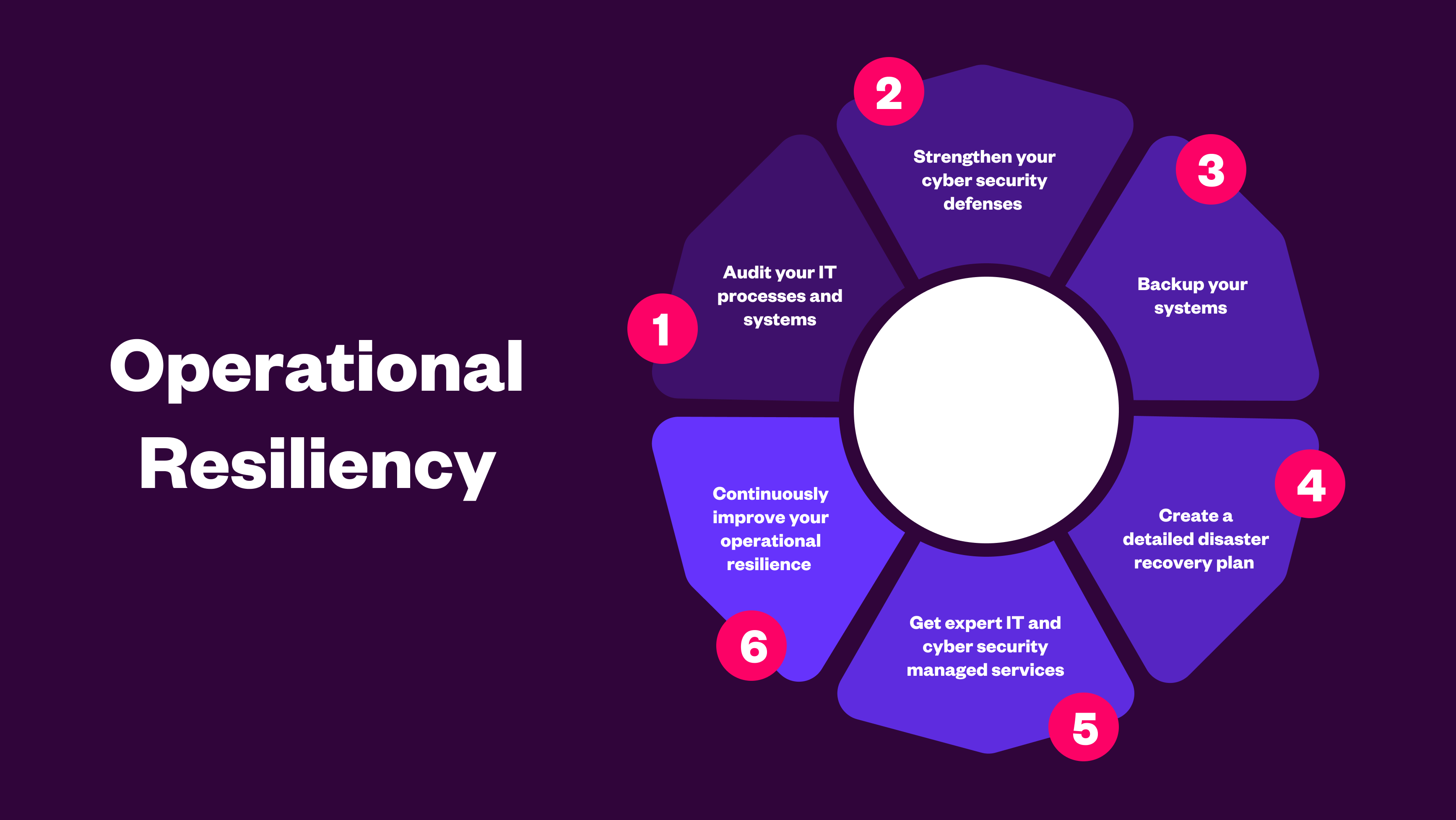
Learn how to build operational resilience against cyber threats, outages, and disruption, with best practices aligned to FCA, PRA, and DORA.
.png)
Vibe coding leads to reliance on familiar patterns, quick fixes, and unchecked dependencies. Learn how these hidden risks expose organisations to cybe...
.png)
AI in cyber security is critical to ensure you stay vigilant against evolving cyber threats, enhance team productivity, and maintain a robust security...
